Tor is an anonymous, secure network that allows anyone to access websites with anonymity. People normally use Tor to access normal websites, but they don’t have to. If you want to set up your own anonymous website, you can create a hidden service Tor site. Your hidden service website runs entirely within Tor, so no one will know who created and runs the website. Only people using Tor can access it, though. Hidden service Tor sites are ideal for anyone who wants to set up a website anonymously, such as political activists in repressive countries.
Not all hidden services have to be websites. You could create an SSH server, IRC server, or any other type of server and offer it as a hidden service on Tor. This tutorial will focus on setting up a hidden Tor site using the Savant web server – which Tor recommends – on Windows. The steps can also be applied to other operating systems and web servers.
How does Tor work ?
From the above image itself one can understand how the Tor works.
For those who did not understand:
" The Tor network runs through the computer servers of thousands of volunteers spread throughout the world. Your data is bundled into an encrypted packet when it enters the Tor network. Then, unlike the case with normal Internet connections, Tor strips away part of the packet's header, which is a part of the addressing information that could be used to learn things about the sender such as the operating system from which the message was sent.
Finally, Tor encrypts the rest of the addressing information, called the packet wrapper. Regular Internet connections don't do this either.
The modified and encrypted data packet is then routed through many of these servers, called relays, on the way to its final destination.The roundabout way packets travel through the Tor network is akin to a person taking a roundabout path through a city to shake a pursuer.
Each relay decrypts only enough of the data packet wrapper to know which relay the data came from, and which relay to send it to next. The relay then rewraps the package in a new wrapper and sends it on.
The layers of encrypted address information used to anonymize data packets sent through Tor are reminiscent of an onion, hence the name. That way a data packet's path through the Tor network cannot be fully traced.
Some regular Internet data packets are encrypted using a protocol called Secure Socket Layer (SSL) or its newer, stronger cousin Transport Layer Security (TLS). For example, if you submit your credit card information to an online store, that information travels across the network in an encrypted state to prevent theft.
However, even when you use SSL or TLS, it's still possible for others to intercept those packets and see the information's metadata — who sent that encrypted information and who received it — because the addressing wrappers in SSL or TLS are not encrypted. In Tor, they are, which hides the sender and receiver of a given transmission.
Further, if you use the Tor Browser to visit a website that does not use encryption to secure users' connections, then your data packet will not be encrypted when it makes the final hop from the last Tor relay to the website's server. That's because the data packet's destination lies outside the Tor network. So it's best to be sure that a website offers some kind of SSL or TLS encryption, usually denoted by an "https" instead of simply "http" in the Web address, before trying to access it anonymously. "
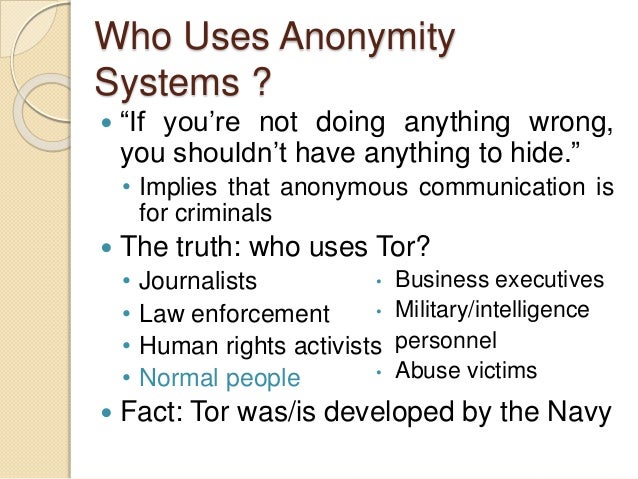
Who uses Tor ?
Tor was originally designed, implemented, and deployed as a third-generation onion routing project of the Naval Research Laboratory. It was originally developed with the U.S. Navy in mind, for the primary purpose of protecting government communications. Today, it is used every day for a wide variety of purposes by the military, journalists, law enforcement officers, activists, and many others. Here are some of the specific uses :
- Normal people use Tor
- Journalists and their audience use Tor
- Law enforcement officers use Tor
- Activists & Whistleblowers use Tor
- High & low profile people use Tor
- Business executives use Tor
- Bloggers use Tor
- Militaries use Tor
- IT Professionals use Tor

%3F.png)
No comments:
Post a Comment